When a customer designs a product in your configurator, they are not just browsing — they are sharing preferences, creating intellectual property, and in many cases providing personal data. That data needs to be handled with the same rigour you apply to payment information and customer accounts. Yet security and privacy considerations are often overlooked during configurator evaluation, overshadowed by discussions about 3D rendering quality and pricing logic.
According to IBM's Cost of a Data Breach Report, the average cost of a data breach reached $4.88 million in 2024 — a 10% increase over the prior year. For businesses embedding third-party configurators on their storefronts, a breach in the configurator platform is a breach of your customer data. This guide covers the security and privacy considerations that should be part of every configurator platform evaluation.
What Data Do Configurators Collect?
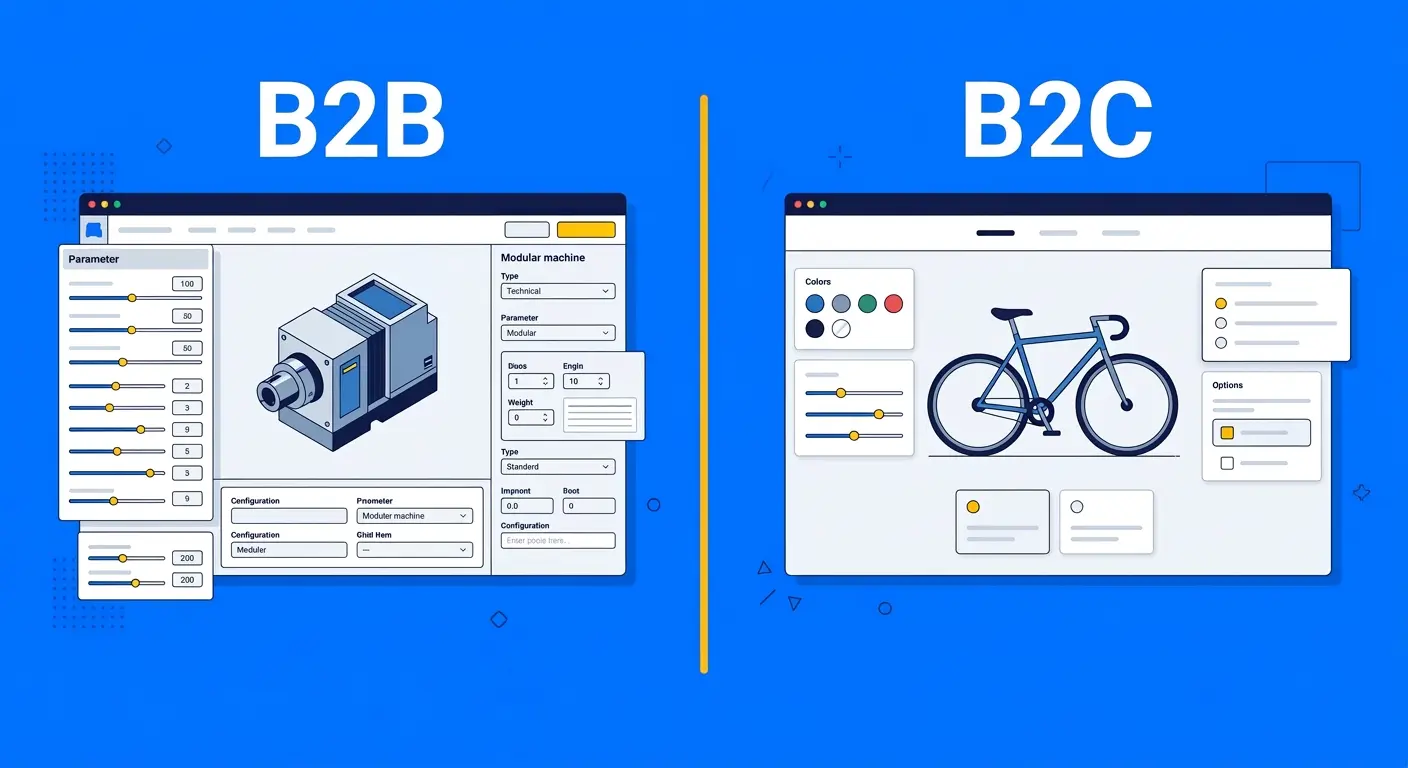
Product configurators collect more data than most businesses realise. Directly, they capture: customer-created designs and specifications, contact information (if saved or shared), pricing calculations and order data, and uploaded files (logos, artwork, reference images). Indirectly, they capture: browsing behaviour and interaction patterns, device information and IP addresses, session data and cookies, and geographic location from IP or browser settings.
For B2B configurators, the data sensitivity increases further. Product specifications may contain proprietary dimensions, custom engineering parameters, or confidential pricing agreements. A B2B configurator that leaks a customer's custom product specifications to a competitor is a business-ending event, not just a compliance issue.
GDPR and CCPA Compliance
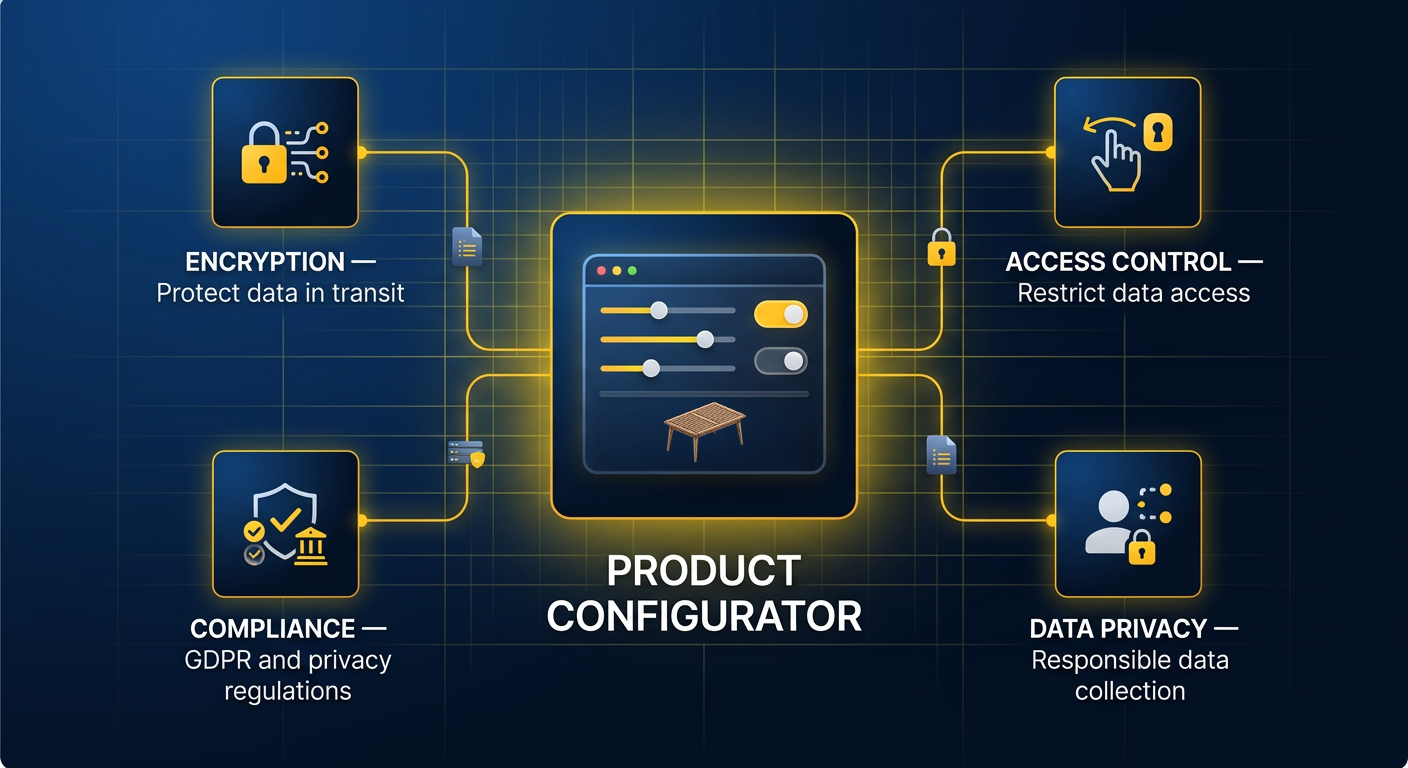
If your customers include European residents, GDPR applies to your configurator. If they include California residents, CCPA applies. Both regulations require explicit consent for data collection, clear disclosure of what data is collected and how it is used, the ability for customers to request deletion of their data, and data processing agreements with third-party platforms (including your configurator vendor).
GDPR Enforcement Tracker data shows that fines have exceeded €4.5 billion since the regulation took effect, with third-party data processing violations among the most common triggers. When evaluating a configurator platform, ask specifically: where is customer data stored, who has access, what is the data retention policy, and will the vendor sign a Data Processing Agreement (DPA)?
Secure Embed Practices
Most configurators are embedded on third-party websites via iframes. This embed model introduces specific security considerations. The iframe should be served over HTTPS with valid TLS certificates. Content Security Policy (CSP) headers should restrict what the embedded content can do — preventing it from accessing the parent page's DOM, cookies, or local storage. The sandbox attribute should limit iframe capabilities to only what is necessary (allowing scripts and same-origin access, but blocking top-level navigation and form submission to external URLs).
Cross-origin communication between the iframe and the parent page should use the postMessage API with strict origin validation. A configurator that requires you to disable CSP headers or remove iframe sandboxing is a red flag. The headless commerce approach can mitigate some of these concerns by rendering the configurator within your own domain, but the data still flows to the configurator platform's servers.
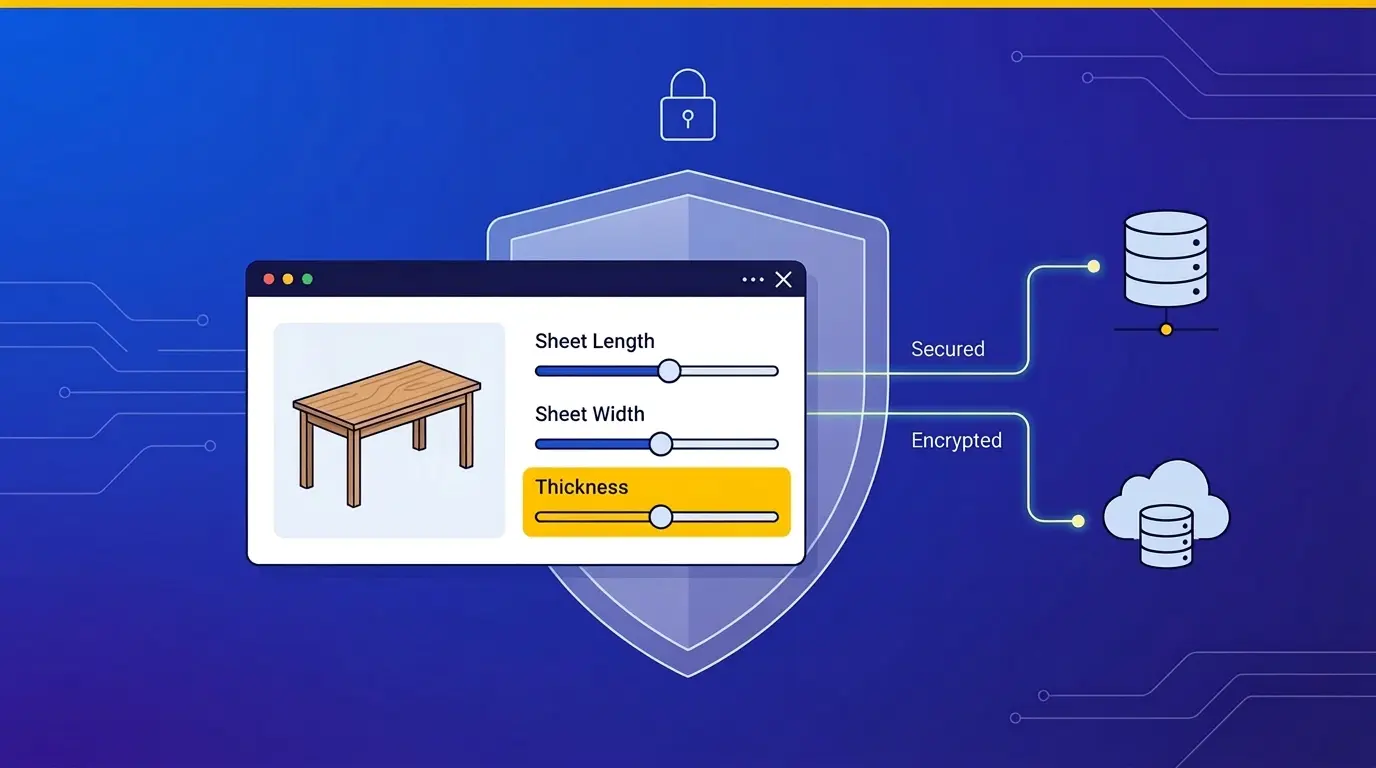
Data Encryption
Data encryption should be non-negotiable at two levels: in transit and at rest. In transit means all data exchanged between the customer's browser, your website, and the configurator platform is encrypted via TLS 1.2 or higher. At rest means data stored on the configurator platform's servers is encrypted using AES-256 or equivalent. This includes configuration data, customer uploads, and any cached renders.
For particularly sensitive applications — military contractors, medical device manufacturers, high-value luxury brands — end-to-end encryption may be required, where the configurator platform itself cannot decrypt customer data. This is a niche requirement, but one worth understanding when evaluating platforms for sensitive industries.
Intellectual Property Protection
Product configurators display your product designs, engineering parameters, and pricing logic to the world. This creates IP concerns that go beyond data privacy. Can a competitor use your configurator to reverse-engineer your product specifications? Can someone scrape your configurator to extract your pricing model?
Mitigations include: obfuscating parametric rules so raw formulas are not exposed to the browser, rate limiting API access to prevent automated scraping, watermarking 3D renders to deter screenshot-based copying, and restricting configuration export to authenticated users. The no-code vs custom-built decision also affects IP protection — custom-built configurators can implement proprietary logic server-side, while no-code platforms may expose more logic to the client.
Enterprise Security Requirements
Enterprise buyers evaluate configurator platforms against formal security frameworks. The most commonly requested certifications include SOC 2 Type II (audited controls for security, availability, and confidentiality), ISO 27001 (information security management system), and penetration testing reports (third-party security assessments conducted at least annually).
Beyond certifications, enterprise procurement teams ask about: incident response procedures, business continuity and disaster recovery plans, employee background checks and access controls, vulnerability disclosure programs, and subprocessor management (does the configurator vendor use third-party services that also access your data?). The platform selection guide covers these evaluation criteria in detail.
Data Residency and Sovereignty
Where your data physically resides matters for compliance. GDPR restricts transfer of EU personal data to countries without adequate data protection laws. Some industries (healthcare, government, financial services) have additional data residency requirements. Ask your configurator vendor: in which regions are servers located, can you choose your data region, and does the vendor use multi-region replication that might move data across borders?
How Configurator.tech Handles Security
Configurator.tech takes security seriously at every level. The platform serves all content over HTTPS with TLS 1.3, encrypts data at rest with AES-256, supports secure iframe embedding with proper CSP headers, and provides API authentication via OAuth 2.0. Our privacy policy details our data handling practices, and we provide DPAs for enterprise customers.
Have specific security requirements? Contact our team to discuss your compliance needs and review our security documentation.